Vulnerability Disclosure Policy
Introduction
Kyocera Document Solutions (referred to as "Kyocera," hereafter) is committed to providing secure products and services (referred to as "Products," hereafter) such as MFPs, printers, solutions, and applications.
Cyberattacks have become more severe and sophisticated around the world. Kyocera constantly monitors these advanced cyberattacks to reduce cybersecurity risks and enhance customers’ cybersecurity and privacy when using our Products. Under these circumstances, our commitment to customers is for us to make a vulnerability response in a timely and efficient manner from the initial investigation up to the resolution of reported vulnerability issues. This commitment enables our customers to use our Products securely and with ease.
Based on the above, we comply with the Vulnerability Disclosure Policy and the Incident Handling Policy, as explained below.
■Incident Handling Policy
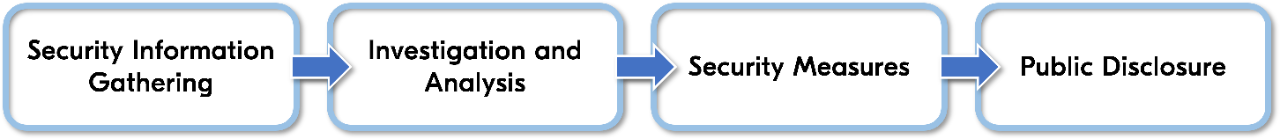
Once a vulnerability is discovered, Kyocera focuses on responding promptly and appropriately, including responding to customers based on security vulnerability information. PSIRT (*1) generally proceeds in the following four steps: (1) gathering and sharing security vulnerability information, (2) investigating security issues and analyzing their impact on our Products, (3) taking security measures against vulnerabilities, and (4) announcing to the public.
(1) Gathering and sharing security vulnerability information
Kyocera checks security information using official open databases of vulnerability information such as CVE, JPCERT and gathers security information from the press, such as newspapers and the Internet. More information is also provided by contacting the customer’s nearest sales company or by inter-office members.
CVE: Common Vulnerabilities and Exposures
JPCERT: Japan Computer Emergency Response Team
(2) Investigating security issues and analyzing their impact on our Products
We investigate and analyze the phenomenon’s effects when a vulnerability is exploited and the difficulty and conditions when a malicious attacker tries to exploit a vulnerability.
(3) Taking security measures against vulnerabilities
After the investigation and analysis, if the results indicate that there is an impact, the development division continues to prepare technical and operational measures, such as applying security patches.
(4) Announcing to the public
We announce our security measures on the Kyocera website, the PSIRT contact window, sales companies, or a service person.
We value dialogue with vulnerability reporters, handle reported vulnerability information in good faith, and fulfill our responsibility by disclosing vulnerability information in a timely and appropriate manner.
■Circumstances
The Vulnerability Disclosure Policy is applied to include the following circumstances:
- A potential vulnerability affecting Products is disclosed to the public.
- A potential vulnerability existing in Products is reported by an external third party.
- A vulnerability impacting released Products is discovered internally.
■Vulnerability Handling Scope
Kyocera considers any individual issues caused by including some weakness in coding or configuration that leads to your vulnerable design are not our vulnerability. We value vulnerability information submitted by reporters. However, whether the reported vulnerability information applies to the vulnerability handling scope will be determined by Kyocera PSIRT.
(*1) See "PSIRT" described in Kyocera's product policy.
Reporting
We encourage you to report vulnerability information that can provide us with significant information that helps improve the security of Products for customers. Before submission of a vulnerability report, please read this Vulnerability Disclosure Policy thoroughly and follow the process described in the following section (i.e., What to expect) in compliance with this policy. Please also note that we do not have a bug bounty program, so you cannot request monetary compensation based upon acknowledgment of the reported vulnerability.
■Contact
If If a vulnerability is discovered in our Products, submit your vulnerability report using the reporting form below. However, if you do not wish to directly contact Kyocera, we recommend submitting your report through the Coordination Center in your country (i.e., CERT/CC) (*2).
■Content
If possible, please submit your report containing the following detailed information:
- Reporter's name and contact information
- Name of the product that contains the potential vulnerability
- The product version that contains the potential vulnerability
- Type of the potential vulnerability (e.g., Information Disclosure, Privilege Escalation, Remote Code Execution, Print Job Manipulation, etc.)
- Impact of the potential vulnerability
- Steps in the specific and detailed process to reproduce the potential vulnerability
- The circumstance that an attacker requires to exploit the vulnerability
- Proof-of-concept code
- Public, third-party reports of vulnerabilities (i.e., references)
- Date when you have discovered the vulnerability
- Others, additional information
(*2) The Coordination Center coordinates incident response related to stakeholders in your country in the event of an incident.
What to expect
After a vulnerability is reported to Kyocera PSIRT, we acknowledge receipt of the vulnerability report. We handle the process according to the following phases:
■Receipt
In the receipt phase, a vulnerability reporter receives acknowledgement within three (3) of our working days. The next correspondence is determined upon completion of our initial investigation. We will keep you informed of our vulnerability analysis status.
■Verification
In the verification phase, we need to confirm with the respective development divisions for any reported vulnerability. We investigate and analyze the phenomenon's effects when a vulnerability is exploited and the difficulty and conditions when a vulnerability is exploited. We ask that you provide us with a reasonable amount of time (at least 90 days from the acknowledgement) to resolve the issue before you disclose it publicly.
■Remediation
In the remediation phase, the respective development divisions complete vulnerability analysis, such as the vulnerability's potential impact on our Products, possible effects when the vulnerability is exploited, and the difficulty and conditions when a malicious attacker attempts to exploit the vulnerability and validate software remediation, mitigation, and workaround. Based upon the results, the timeline will be determined so we can take temporary and permanent security measures, respectively. If a vulnerability significantly impacts the global markets and takes time to remediate, alternative mitigation measures will be offered to customers. We will provide customers with adequate security measures as soon as possible and be as transparent as possible about the steps we take during the remediation process, including on issues or challenges that may delay resolution. We will communicate closely with the vulnerability reporter.
■Publication
We are responsible for the appropriate disclosure of vulnerability information and extend the same responsibility to reporters. If Kyocera PSIRT determines that the vulnerability information is critical to customers, like when there is a possibility of personal information leaks, we will publish security-related information (i.e., the advisory) on our security page of the Kyocera company global website and Kyocera Group company website in your country. For any public release, please coordinate with Kyocera PSIRT or Computer Emergency Response Team Coordination Center (CERT/CC) (in case you contact CERT/CC in your country). Note that we create the disclosure contents based on the coordination.
Guidance
You must not:
- Violate laws/regulations/standards enacted in respective countries/regions.
- Share or re-distribute any data obtained through our Products to third parties.
- Submit the report by using a product obtained improperly through a malicious person.
- Attempt to contact us utilizing vulnerable communication.
- Report any vulnerabilities related to Denial of Services (DoS or DDoS), e.g., overwhelming our service with a high volume of requests.
- Submit the report on Products that are still running outdated software versions.
- Submit the report on Products that are not brought in line with best practices.
- Submit the report on TLS configuration weaknesses e.g., TLS1.0 support.
- Use social engineering attacks.
- Demand monetary compensation to disclose any vulnerabilities.
You must:
- Be compliant with all relevant laws/acts, standards, data protection, and privacy laws.
- Report vulnerability information only for undisclosed vulnerabilities in the Products.
- Securely delete all data used during your vulnerability investigation/analysis/research as soon as it is no longer required.
License to Reported Vulnerability Information
Kyocera does not claim any ownership rights to the information included in the reported Vulnerability Disclosure under this Policy, including, but not limited to, any data, text, material, program code, suggestion and recommendation received from the reporter (“Reported Vulnerability Information”). By providing any Reported Vulnerability Information to Kyocera, the reporter ;
- grants us the following non-exclusive, irrevocable, perpetual, royalty-free, worldwide, sub-licensable license to the intellectual property in the Reported Vulnerability Information:
(i) to use, review, assess, test, and otherwise analyze the Reported Vulnerability Information; and
(ii) to reproduce, modify, distribute, display and perform publicly, and commercialize and create derivative works of the Reported Vulnerability Information and all its content, in whole or in part, for the purpose of fixing the reported vulnerabilities, improving Products, and marketing, sale and promotion of such improved Products;
- agrees to sign any documentation that may be required for us or our designees to confirm the rights the reporter granted above;
- understands and acknowledges that we may have developed or commissioned materials similar or identical to the Reported Vulnerability Information, and the reporter waives any claims or rights it may have resulting from any similarities to the Reported Vulnerability Information;
- understands and acknowledges that it is not guaranteed any compensation or credit for Reported Vulnerability Information; and
- represents and warrants that it hasn’t included any of personal data in Reported Vulnerability Information, it hasn't used any information or intellectual property owned by a third party in violation of legal or contractual requirements, and that the reporter has the legal right to provide the Reported Vulnerability Information to us subject to this Policy.



